Exploring the Innovations of Embedded Development
The World of Embedded Development
Embedded development is a fascinating field that plays a crucial role in powering the devices we use every day. From smartphones to smart home appliances, embedded systems are at the heart of modern technology.
So, what exactly is embedded development? In simple terms, it involves designing and programming small computing systems that are embedded within larger devices or machinery. These systems are dedicated to specific functions and operate with minimal human intervention.
One of the key challenges in embedded development is optimizing performance while working within constraints such as limited processing power, memory, and energy consumption. Developers must carefully design efficient algorithms and code to ensure that the embedded system functions reliably and effectively.
Embedded developers work with a variety of hardware platforms and programming languages, depending on the requirements of the project. Common languages used in embedded development include C, C++, and assembly language. They also utilize specialized tools and software to debug and test their code thoroughly.
As technology continues to advance, the demand for skilled embedded developers is on the rise. Companies across industries rely on these experts to create innovative solutions that drive progress and improve efficiency. Whether it’s designing wearable devices or implementing IoT solutions, embedded developers are at the forefront of innovation.
In conclusion, embedded development is a dynamic and rewarding field that offers endless opportunities for creativity and problem-solving. As we look towards a future filled with smart devices and interconnected systems, the role of embedded developers will only become more vital in shaping our digital world.
Top 8 Frequently Asked Questions About Embedded Development
- What is embedded development?
- What programming languages are commonly used in embedded development?
- How does embedded development differ from traditional software development?
- What are the key challenges faced by embedded developers?
- Which industries rely heavily on embedded systems?
- What tools and software are essential for embedded development?
- How can one start a career in embedded development?
- What are some examples of popular devices that use embedded systems?
What is embedded development?
Embedded development refers to the process of designing and programming small computing systems that are integrated within larger devices or machinery to perform specific functions autonomously. These embedded systems are dedicated to executing predefined tasks efficiently with minimal human intervention. Embedded development involves optimizing performance within constraints such as limited processing power, memory, and energy consumption. Skilled developers in this field work with a variety of hardware platforms and programming languages to create reliable and effective solutions for a wide range of applications in modern technology.
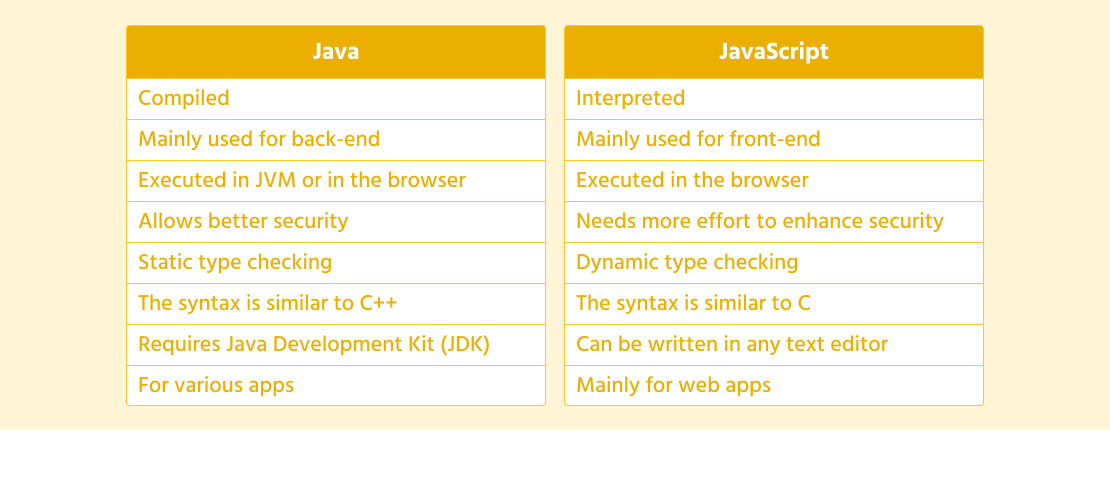
What programming languages are commonly used in embedded development?
In the realm of embedded development, several programming languages are commonly utilized to craft efficient and reliable systems. Among the popular choices are C, C++, and assembly language. These languages offer developers the flexibility and control needed to optimize performance while working within the constraints of limited resources typical in embedded systems. By leveraging these languages, developers can create robust code that powers a wide array of devices and machinery, showcasing the versatility and power of embedded development in today’s technological landscape.
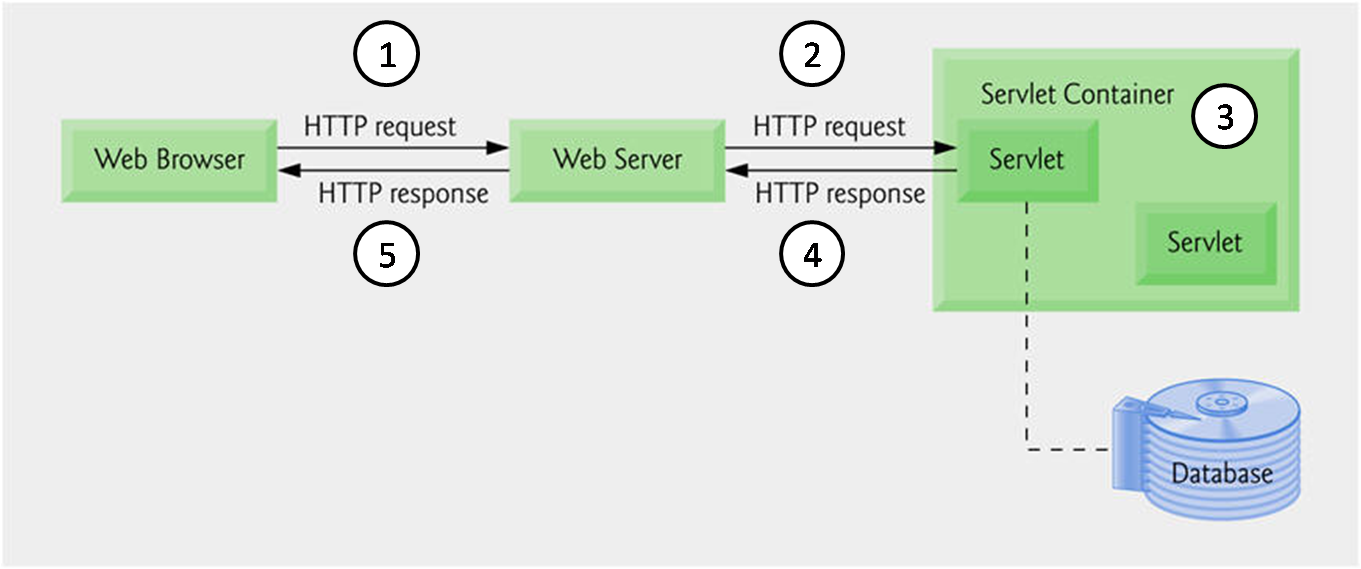
How does embedded development differ from traditional software development?
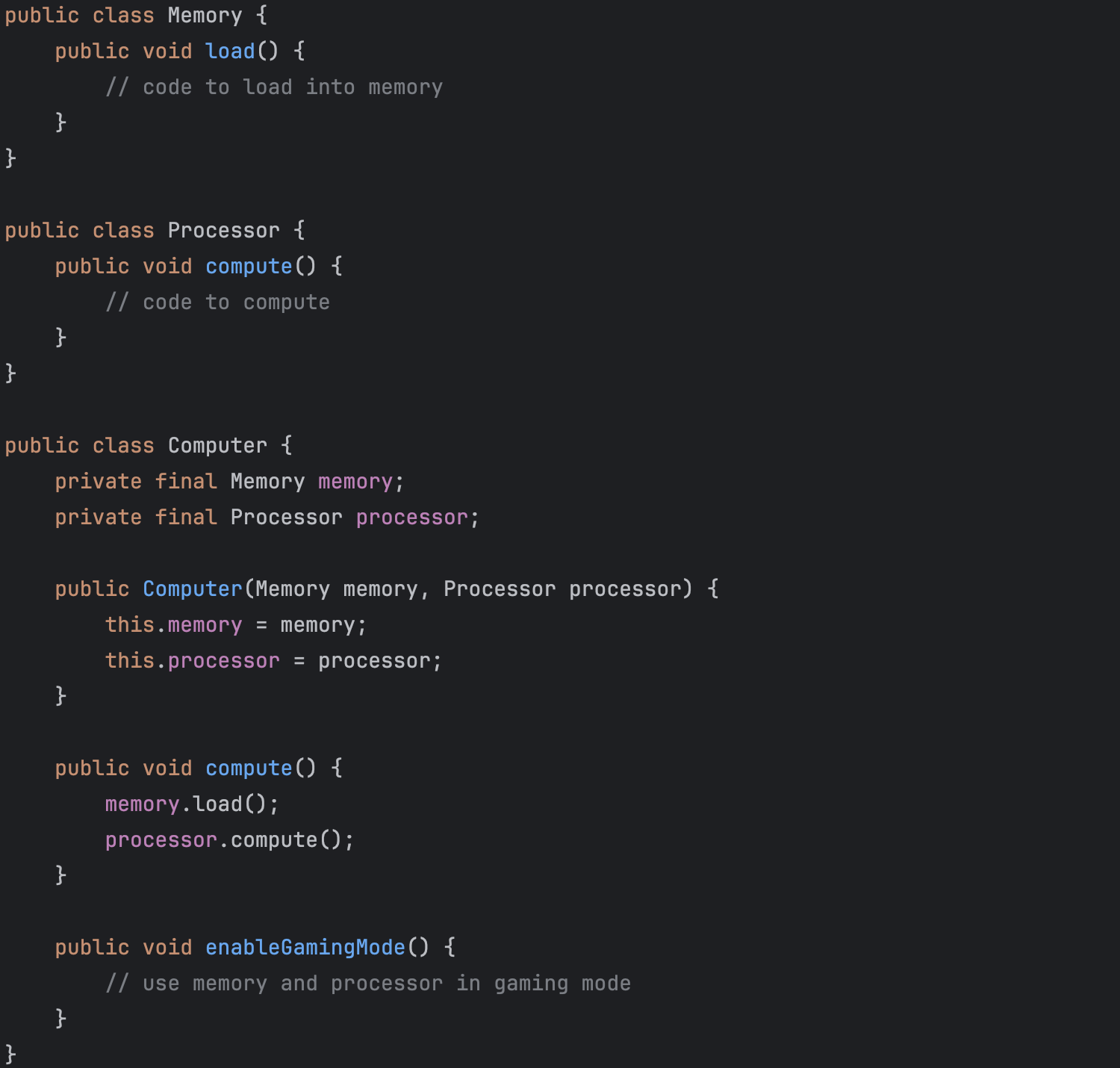
In the realm of technology, the distinction between embedded development and traditional software development lies in their respective focuses and applications. Embedded development involves creating software that is specifically tailored to operate within embedded systems, such as microcontrollers or IoT devices, where space, power, and processing constraints are prevalent. In contrast, traditional software development typically revolves around designing applications for general-purpose computing devices like computers and smartphones, with a broader scope and fewer hardware limitations. The specialized nature of embedded development necessitates a deep understanding of hardware-software interactions and optimization techniques to ensure efficient performance within constrained environments.
What are the key challenges faced by embedded developers?
Embedded developers face several key challenges in their work. One of the primary challenges is optimizing performance within the constraints of limited resources such as processing power, memory, and energy consumption. They must carefully design efficient algorithms and code to ensure that the embedded system operates reliably and effectively. Additionally, staying up-to-date with rapidly evolving technology and hardware platforms is essential for embedded developers to create innovative solutions that meet the demands of modern devices and applications. Debugging and testing code thoroughly to ensure functionality and security are also critical challenges faced by embedded developers in their day-to-day work.
Which industries rely heavily on embedded systems?
Various industries rely heavily on embedded systems to power their products and services. The automotive industry utilizes embedded systems in vehicles for functions such as engine control, navigation systems, and driver assistance features. The healthcare sector employs embedded systems in medical devices like pacemakers, insulin pumps, and monitoring equipment to improve patient care. Additionally, the consumer electronics industry incorporates embedded systems into smartphones, smart TVs, and home appliances to deliver enhanced functionality and connectivity. Industrial automation relies on embedded systems for controlling machinery and optimizing manufacturing processes. Overall, industries such as automotive, healthcare, consumer electronics, and industrial automation heavily depend on embedded systems for innovation and efficiency in their operations.
What tools and software are essential for embedded development?
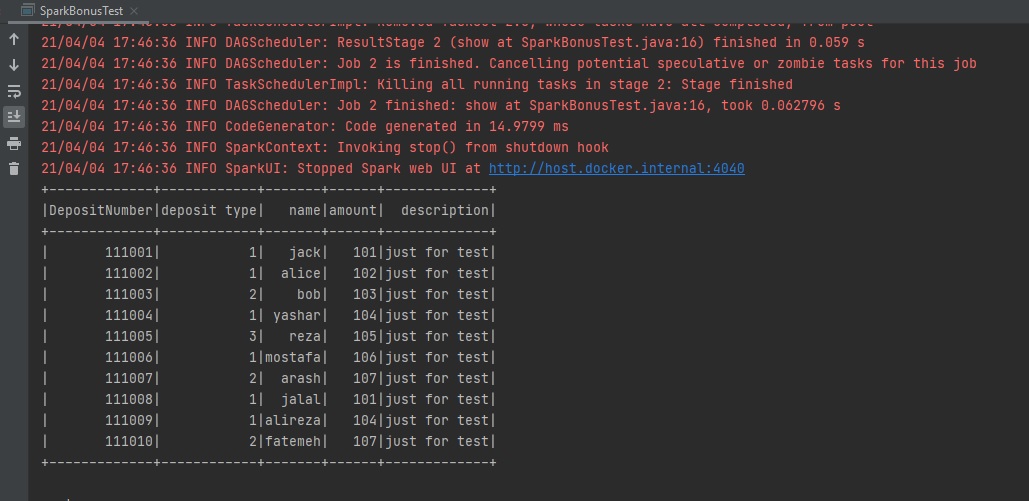
When it comes to embedded development, having the right tools and software is crucial for success. Essential tools for embedded development include integrated development environments (IDEs) like Eclipse or Visual Studio, which provide a comprehensive platform for writing, compiling, and debugging code. Additionally, software tools such as compilers, debuggers, and simulators are essential for testing and optimizing code for embedded systems. Version control systems like Git help manage code changes efficiently, while hardware debugging tools such as JTAG interfaces enable developers to troubleshoot issues at the hardware level. Overall, a well-equipped toolbox of software and tools is essential for streamlining the development process and ensuring the reliability of embedded systems.
How can one start a career in embedded development?
To start a career in embedded development, individuals can begin by gaining a strong foundation in computer science and programming languages such as C and C++. Acquiring knowledge of electronics and microcontrollers is also essential. Engaging in hands-on projects, such as building simple embedded systems or participating in coding competitions, can help develop practical skills. Pursuing internships or entry-level positions in companies that specialize in embedded systems is another valuable step towards entering the field. Continuous learning and staying updated on industry trends through online courses, workshops, and networking with professionals can further enhance one’s prospects in starting a successful career in embedded development.
What are some examples of popular devices that use embedded systems?
Embedded systems are ubiquitous in our daily lives, powering a wide range of popular devices that we rely on regularly. Some examples of these devices include smartphones, smartwatches, digital cameras, home appliances like smart thermostats and refrigerators, automobile navigation systems, medical devices such as pacemakers and insulin pumps, and industrial machinery like robotics and automation systems. These devices leverage embedded systems to perform specific functions efficiently and reliably, showcasing the versatility and importance of embedded development in modern technology.